Small Business Cyber Security Health Check
Find your security gaps before attackers do. Covers passwords, backups, updates, staff awareness, and incident readiness.
View Small Business Health CheckSmall Business
1 in 5 small businesses don't survive a cyber attack. Regulatory expectations are rising. Are you sure you have everything in place?
Cyber criminals have shifted focus. Large enterprises have security teams, budgets, and sophisticated defences. Small businesses don't—which makes you the easier target. 43% of all cyber attacks now target small businesses, and the attacks that cause the most damage aren't sophisticated. They're simple: a convincing email, a weak password, a backup that wasn't tested.
1 in 5 small businesses that suffer a cyber attack close within 12 months. Not because they were hit by nation-state hackers—but because they couldn't recover. Systems locked by ransomware. Customer data stolen. Weeks of downtime. Reputation destroyed. For a small business operating on tight margins, that's often fatal.
Australian businesses are legally required to take "reasonable steps" to protect personal information. If you suffer a breach and can't demonstrate what protections you had in place, penalties can reach $50 million. But the financial penalty isn't the worst part—it's having to notify every affected customer that their data was exposed because you didn't have the basics covered.
Increasingly, businesses won't work with suppliers who can't demonstrate basic security practices. Cyber insurance applications now ask detailed questions about your controls—and claims get denied when businesses can't prove they had protections in place. If you're tendering for contracts, responding to supplier questionnaires, or renewing insurance, you need to know where you stand.
The Tax Practitioners Board, ASIC, AHPRA, the NDIS Commission, Law Societies—professional regulators across every industry are raising expectations around cyber security. It's no longer optional. If you handle client money, sensitive records, or personal information, your regulator expects you to have controls in place. "I didn't know" is no longer an acceptable answer.
Most small business breaches happen because of fixable gaps—passwords reused across systems, backups that aren't tested, staff who haven't been shown what a phishing email looks like. You don't need an IT department or expensive consultants. You need every gap identified, ranked by risk, with specific actions to fix them.
A guided questionnaire—in plain English, no jargon—that walks through the security controls that actually matter for your business. Passwords. Backups. Email security. Software updates. Staff awareness. Incident readiness. In about 60 minutes, you'll have:
You get a prioritised roadmap—not just findings, but exactly what to do about them. Compare that to the cost of a breach—or the cost of losing a contract because you couldn't answer a supplier security questionnaire.
From first question to final report — here's what the experience looks like.
Enter your business name and track progress across all 11 security domains. Your answers save automatically — close the browser and pick up where you left off any time.

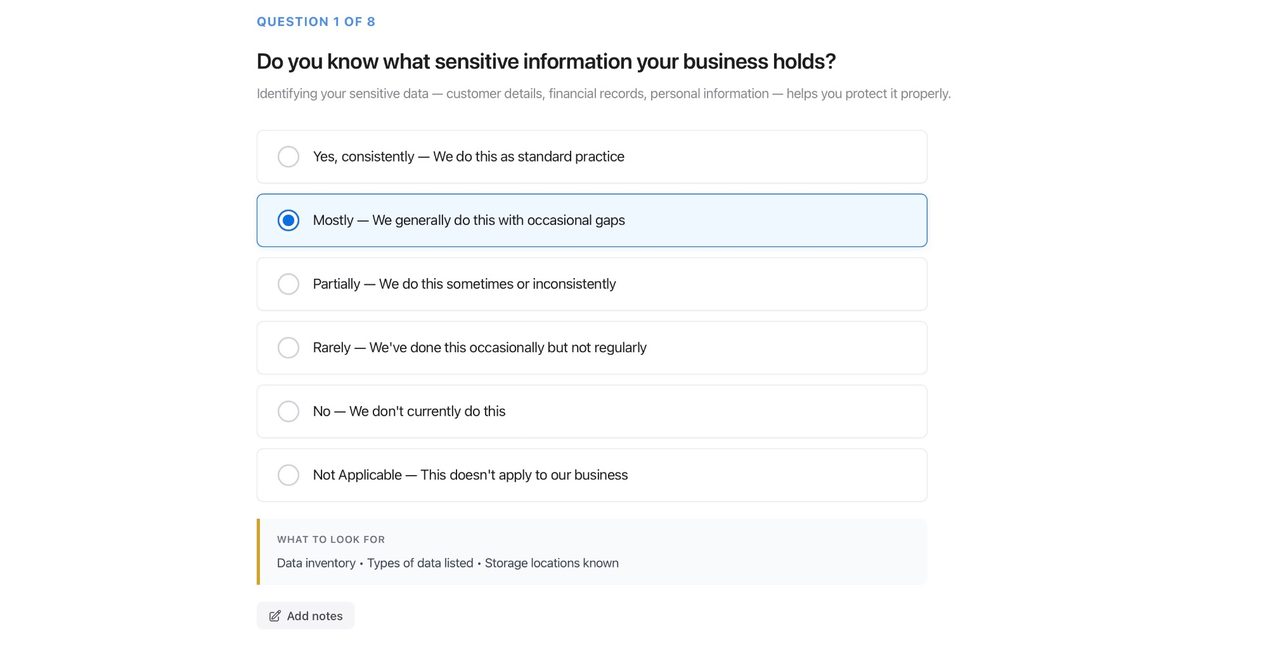
Each question is written for business owners, not IT professionals. A "What to look for" guide is included on every question — you'll always know exactly what a good answer looks like.
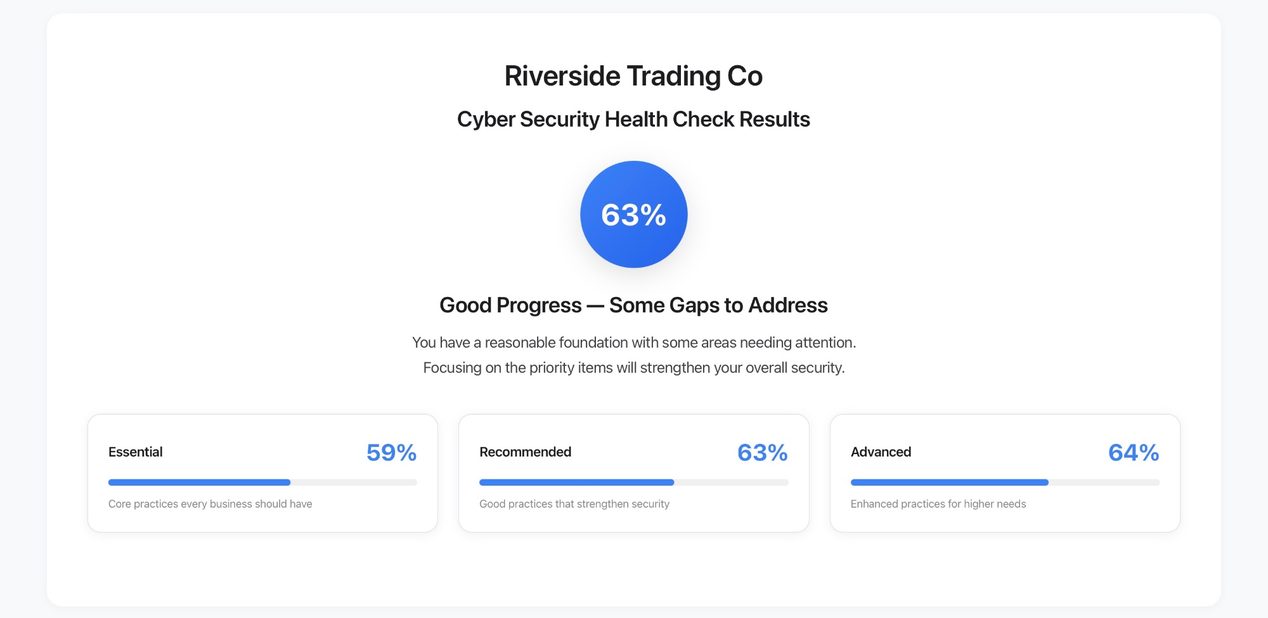
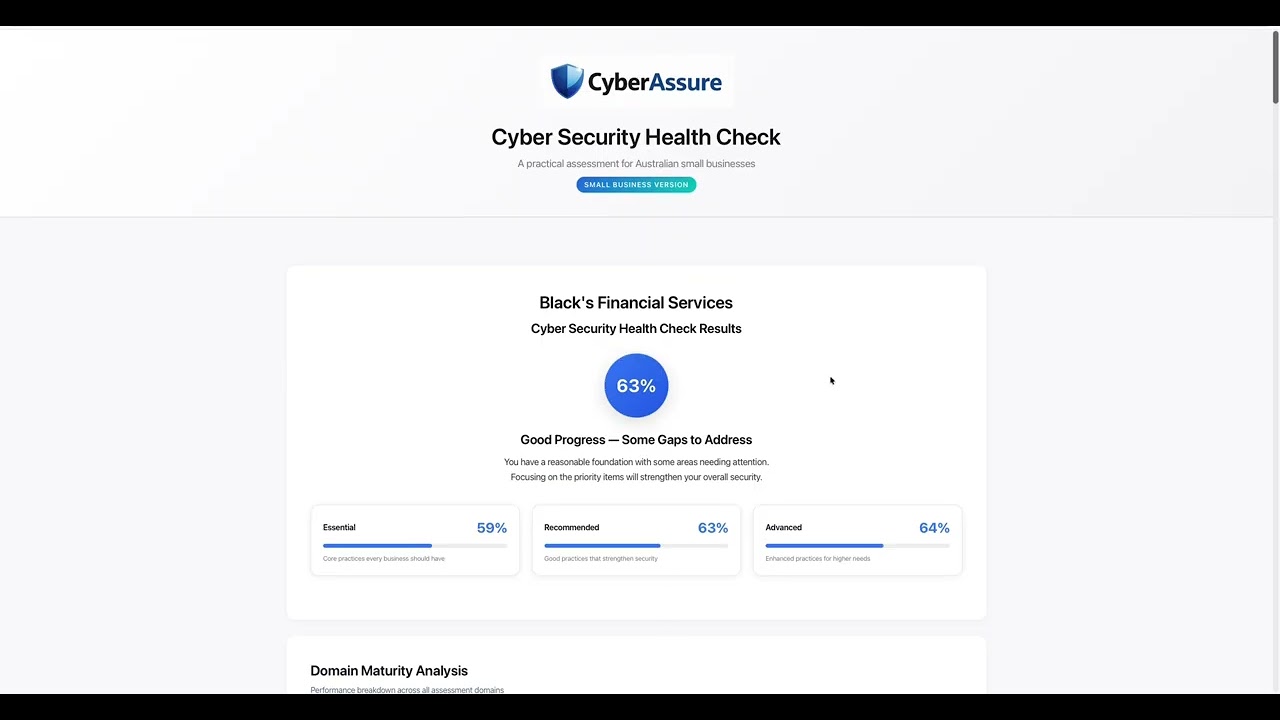
Get an instant overall score with a plain-English rating. Scores are broken down across Essential, Recommended, and Advanced practice levels so you know exactly where to focus first.
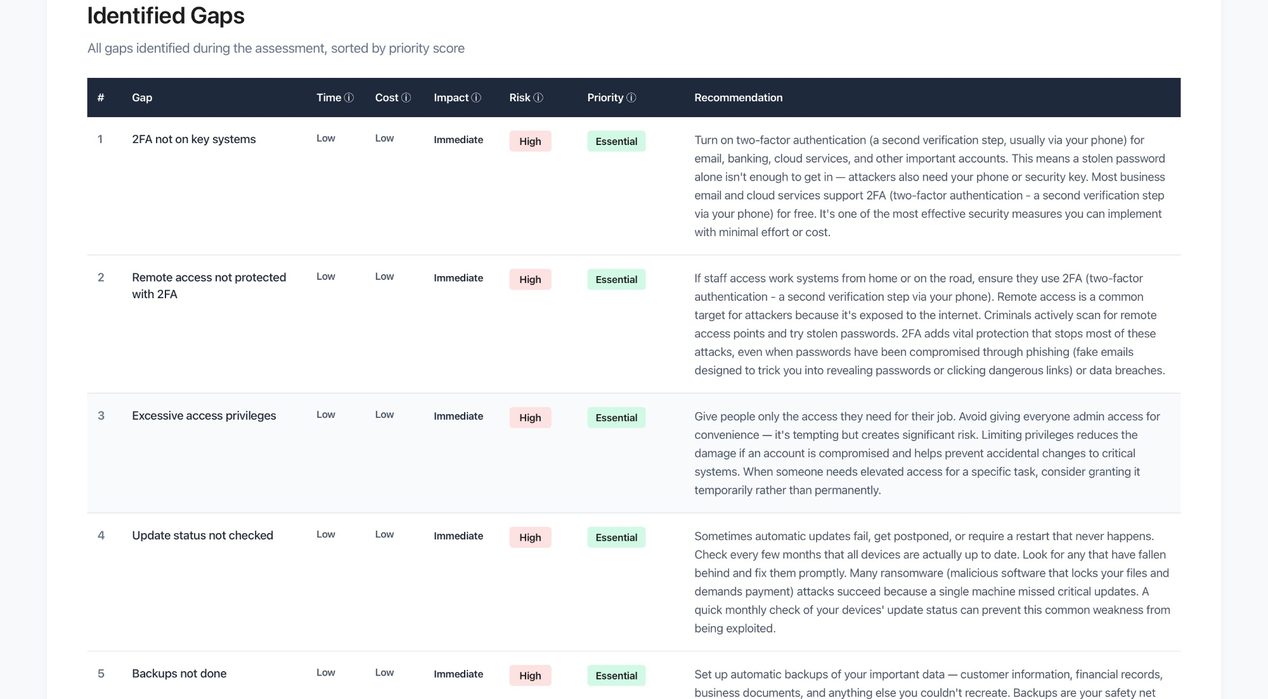
Every gap is ranked by priority with a plain-English recommendation. Time, cost, and impact ratings help you decide what to tackle yourself and what to hand to your IT provider.
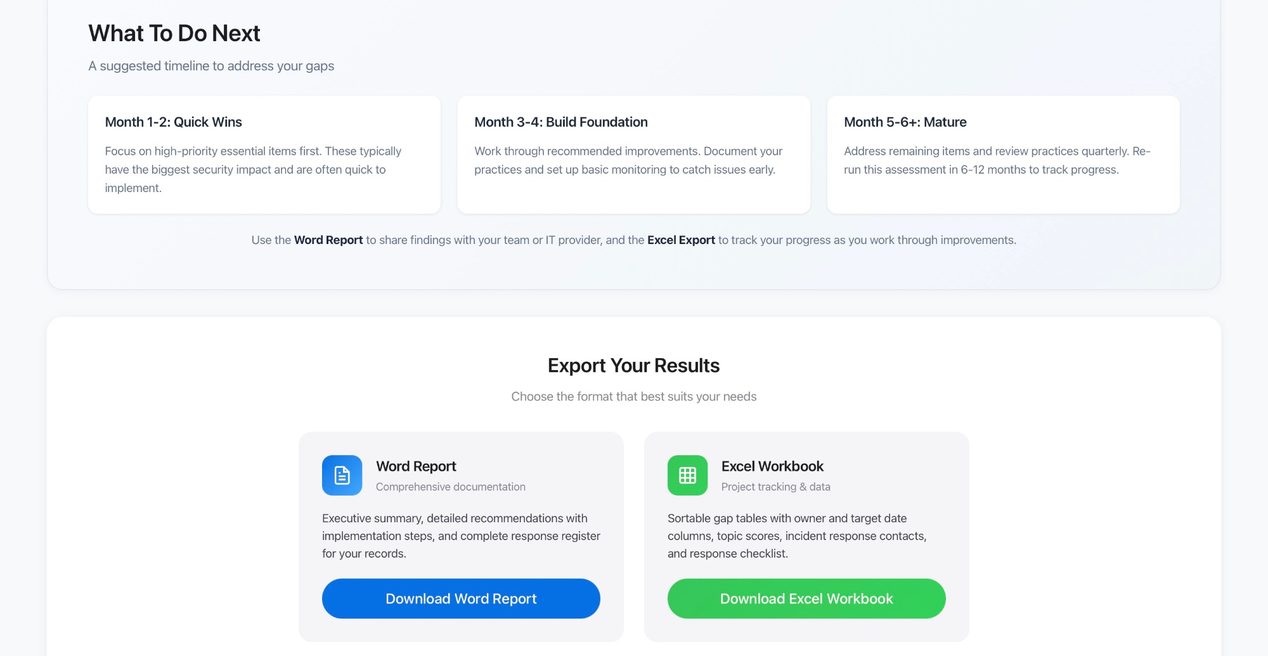
A suggested month-by-month action plan shows you what to fix first, next, and over time. Export a Word report to share with your team or IT provider, and an Excel workbook to track progress.
Every health check generates a comprehensive report you can use immediately. Download a sample below.
Plain-English findings with prioritised recommendations, improvement plan, risk associations, and resources. Share with your IT provider or keep for your records.
Download SampleTwo AI assistants are built into every tool. One helps you understand questions as you go. The other is available the moment you see your results — ready to explain every gap, every action, and every score in plain English.
Included in every health check — bring your own API key
For the first time, small businesses get on-demand security expertise built directly into the tool. No consultants. No jargon. No guesswork. The AI advisor is built in — you connect it using your own Claude API key, and pay only for what you use (typically a few cents per session).
Find your security gaps before attackers do. Covers passwords, backups, updates, staff awareness, and incident readiness.
View Small Business Health CheckATO portal security, Xero/MYOB protection, client TFN handling, BAS fraud awareness, Privacy Act compliance.
View Accounting Practice Health CheckATO Portal security, accounting software protection, TPB Code requirements, client data handling.
View Bookkeeper Health CheckCourt portal security, practice management software, conveyancing fraud prevention, legal privilege considerations.
View Law Firm Health CheckTrust account security, property management software, tenant ID handling, settlement fraud awareness.
View Real Estate Health CheckPRODA/Medicare portal security, clinical software protection, patient records, prescription scam recognition.
View GP Clinic Health CheckPractice management software, Medicare/DVA claims security, patient records, mobile practitioner considerations.
View Allied Health CheckPRODA portal security, client management systems, NDIS Practice Standards alignment, participant data handling.
View NDIS Provider Health CheckCCS system security, childcare management software, children's records, NQS alignment, parent communication.
View Childcare Health CheckLicensee portal security, client portfolio protection, ASIC impersonation awareness, Privacy Act compliance.
View Financial Planning Health CheckSettlement fraud prevention, bank details verification, CRM security, ID document protection.
View Mortgage Broker Health CheckDownload the HTML file, open it in your browser, answer the questions. About 60 minutes. No technical knowledge required—the questions are written in plain English for business owners, not IT professionals. Get a clear picture of your security gaps and what to fix first.
Your data stays private — everything runs locally on your device. Nothing is sent to us.
Find out how the health checks work, what you get, and how your data is protected.